 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
With the growth of BYOD, what security measures can IT take to ensure security of enterprise data – and does MDM have a role?
While mobile device management will always be in use in the enterprise, thankfully, a better option exists. In fact, it seems the only group not excited about BYOD is IT – the ones who have to figure out how to keep sensitive corporate information safe. IT's consternation over BYOD is made worse by the fact that many think mobile device management (MDM) is the only tool available to contain the risks associated with BYOD, which is not the case. MDM will always have a place in the enterprise because BYOD will simply never be the right approach for every employee. However, when it comes to BYOD implementations, MDM is not ideal. Thankfully, a better option exists. Mobile application management (MAM) presents an intriguing option for preparing for and avoiding the hazards of BYOD. Read more, a MUST: http://www.scmarketscope.com/mdm-and-byod-a-square-peg-for-a-round-hole/article/260623/
The BYOD trend will make cyber security more complex Of the tips put forward by IDC, the first one is perhaps the most obvious and perhaps the reasons why the BYOD trend has caused so many headaches. “The consensus is that BYOD is now a given. Whether you want it or not, employees will do your work on their own devices,” says Infosec commentator Stilgherrian. “So your choice is whether to have a policy that acknowledges that and lays out the ground rules, or try to ban it and end up with an infestation of unknown and uncontrolled devices.” However, as many enterprises are currently finding out, controlling and securing data on multiple devices is a lot easier said than done. Read more, a MUST: http://technologyspectator.com.au/byod-security-commandments

|
Scooped by
Gust MEES
|
Si 34% d’entreprises interdisent l’usage de terminaux personnels, elle sont également 55% à appliquer des règles strictes pour encadrer l’accès aux documents professionnels depuis ces appareils.

|
Scooped by
Gust MEES
|
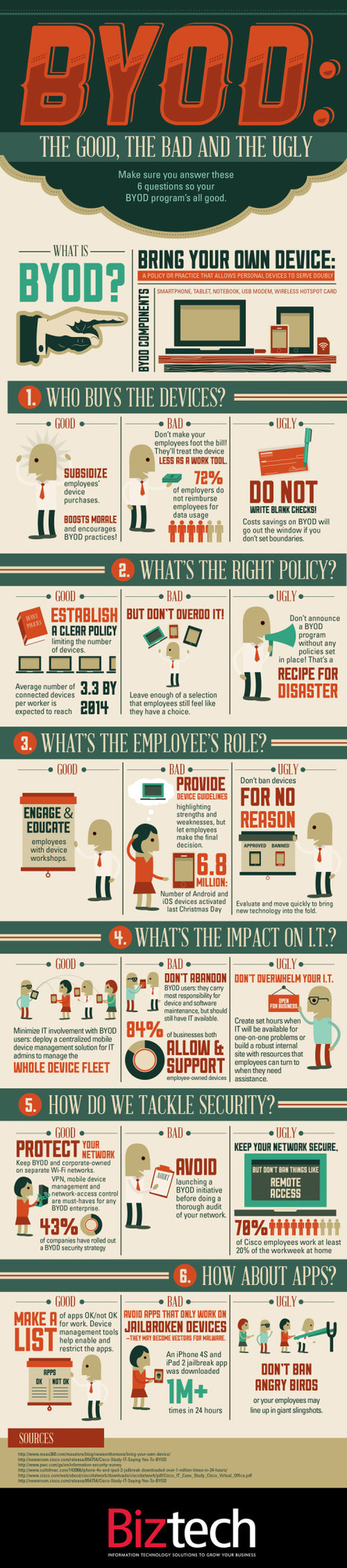
“BYOD” Bring Your own Device. A great idea that can easily turn messy. Biztech has introduced the BYOD: The Good, the Bad and the Ugly infographic asking you to answer 6 easy but important questions before you launch into a BYOD situation. If your company is considering allowing employees to bring their own devices to work, make sure you have a game plan in place. BYOD has freed up many enterprises from the responsibility of exclusively purchasing and maintaining computing devices, such as notebooks, tablets and smartphones, but companies still need to have policies set in place to make things work. BizTech magazine has put together an infographic that highlights six core questions every company should consider before moving forward with BYOD: - Who buys the devices?
- What’s the right policy?
- What’s the employee’s role?
- What’s the impact on IT?
- How do we tackle security?
- How about apps?
For each of these questions, we’ve outlined a good answer, which we’d advise you to follow; a bad answer, which probably isn’t the best way to handle things; and an ugly answer, which should be avoided at all costs. Hopefully, this will help your company remain on the pleasant side of this growing workplace trend.
Gust MEES: please read also my FREE course here - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ Read more: http://www.coolinfographics.com/blog/2012/9/10/byod-the-good-the-bad-and-the-ugly.html
Is IT becoming a consumer product?... Most people are participating in rogue IT without even realizing it. By definition, rogue IT is the unmanaged hardware and software that employees bring into their offices, connect to employers’ networks and use for professional productivity on personal time. At first, it doesn’t sound so bad. By allowing employees to connect to the Wi-Fi with their own devices, companies avoid the cost of providing the hardware. But as we learned from the BYOD toolkit from CIO.gov, BYOD programs aren’t profitable if they are uncontrolled, because problems, like the ones we’ll discuss below, arise. ===> Rogue IT is innovative and efficient for workers, but it’s becoming a real problem for IT managers. Here are four trends that are shaking up IT: <=== Gust MEES: check out also my FREE course about it here - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ Read more: http://www.statetechmagazine.com/article/2012/09/4-rogue-it-trends-watch-out

|
Scooped by
Gust MEES
|
The Norton Cybercrime Report is out for 2012! Cybercrime continues to have far-reaching effects and is increasingly a problem on mobile devices and in our social networks (where we seem to be less vigilant). After surveying more than 13,000 consumers in 24 countries, the researchers found that the numbers of online adults increased by 20 percent from last year, and that cybercrime impacted just under ½ of them in the previous 12 months. The total direct consumer cost was calculated to be $110 billion, slightly down from last year’s $114 billion (USD), with the average cost per victim down approximately 20 percent. The reason the overall cost remains so high is that the pool of victimized online adults grew more rapidly - in other words, less money, but from more victims.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
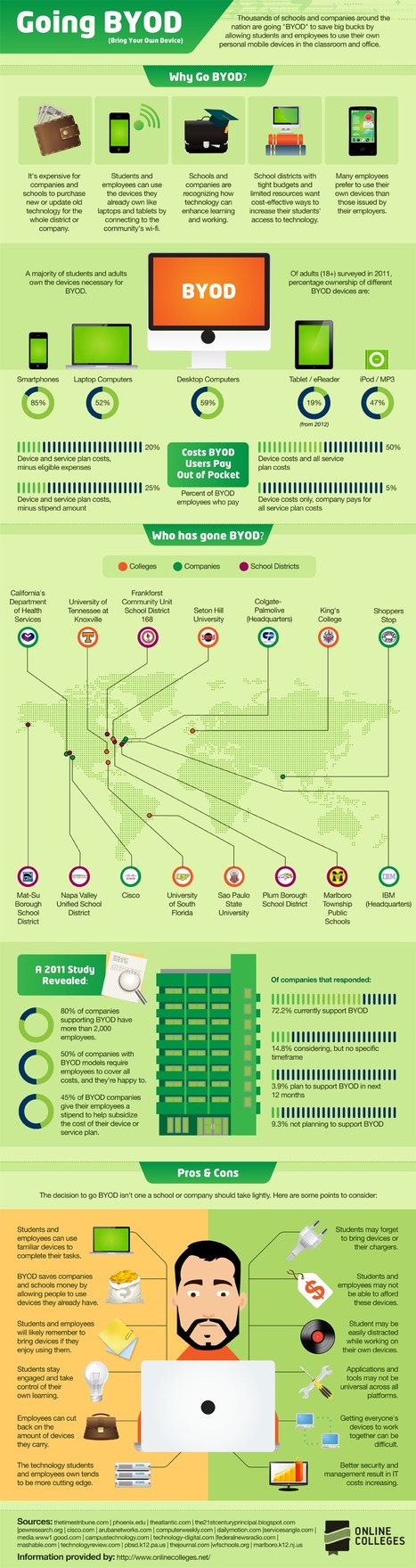
Businesses may no longer be able to turn away employees who want to bring their smartphones and tablets to work, and connect to the corporate network. Even the government acknowledges that it can't prevent the use of personal devices for work-related functions, reports Marcos Colón. With more than 60,000 employees, Cisco Systems has embraced the bring-your-own-device (BYOD) phenomenon, defined as the burgeoning penetration of personal smartphones, tablets and laptops into the workplace. Gust MEES: While using BYOD and Social Media, teachers need to have knowledge of basic IT-Security (they must learn it...)! It's NOT ONLY the IT-Admin's and Technical Coordinator's role! This basic knowledge they should share with their learners to make the community stronger for a more secure Internet... ============================================= Wer A sagt, muss auch B sagen. (Plattdeutsche Variante: De A seggt, mut ok B seggen")
Translation: If you say A, you have to say B as well.
===> Meaning: No half-assed evading or cherry picking. <===
Meaning: If you want or assert A and it turns out to involve B, you have to put up with B too.
Meaning: Follow through [don't wimp out]
Similar: "In for a penny, in for a pound."
Strauss, Emmanuel (1998). Dictionary of European Proverbs. Routledge. p. 957. ISBN 0415160502.
============================================= I suggest to you to visit my FREE Online courses about basic IT-Security here: Bring Your Own Device: Advantages, Dangers, Risks and best Policy to stay secure: - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ My "Thinglink" interactive courses embedded with "Rich-Media" in ONLY ONE IMAGE: - https://www.thinglink.com/scene/296377469991124993#tlsite

|
Scooped by
Gust MEES
|
Nowadays all employees bring their own Internet-aware devices to work. Employers and institutions such as schools think
they can save a lot of money by having their employees or students use their own kit. These devices are often 'powered' by applications downloaded from some kind of App-Store/Market. The applications there should be safe, but are they? What kind of risks do they pose for personal or corporate data? Furthermore, the paper will describe different vectors of attack towards corporate networks and the risk of intractable data leakage problems: for example, encryption of company data on portable devices is by no means common practice. Finally, we offer advice on how to handle BYOD policies in your own environment and if it is really worth it. Maybe 'Windows To Go' - a feature of Windows 8 that boots a PC from a Live USB stick which contains Win8, applications plus Group Policies applied by the admin - is a suitable base model for converting BYOD into a Managed By IT Device. ===> Remember: BYOD isn't coming, it is here already and it is (B)ig, (Y)et (O)utside (D)efence perimeters! <===

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Online Trends and Risks with BYOD [pdf]
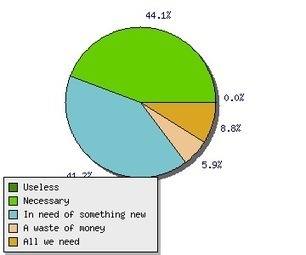
Study from Kaspersky Labs: Digital Consumer’s Online Trends and Risks Modern consumers live a full-scale digital life. Their virtual assets like personal photos and videos, work documents, passwords to access social networking and online banking credentials are of the utmost importance and users are very concerned about safety of such data. We at Kaspersky Lab maintain and expand the leading expertise in IT security risks, malware and vulnerabilities in order to protect consumers in the best possible way. To better understand our customers, their computer and Internet usage patterns and attitudes towards security and the safety of data, we initiated a study into this valuable information. Although users acknowledge the existence of various online threats, a significant share of them are reckless in terms of security. ===> Even now 16% of laptop owners, 50% of Macbook users and 65% (!) of smartphone owners do not use any kind of security software on their devices. <=== Check out also http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/ to get a maximum of informtion about BYOD! Gust MEES: a MUST READ for people using BYOD! Read more [pdf]: http://www.kaspersky.com/downloads/pdf/kaspersky_lab_consumer_survey_report_eng_final.pdf

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
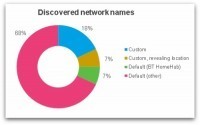
Do you always turn WiFi off on your smartphone before leaving the house or work? You might think there's no harm in having WiFi turned on but not connected to a network, but that's not necessarily the case. A wireless device goes through a discovery process in which it attempts to connect to an available wireless network. This may either be ‘passive’ - listening for networks which are broadcasting themselves - or ‘active’ - sending out probe request packets in search of a network to connect to. Most devices use both passive and active discovery in an attempt to connect to known/preferred networks. So it's very likely that your smartphone is broadcasting the names (SSIDs) of your favourite networks for anyone to see. ===> An ‘evil twin’ attack could even accomplish this without needing any knowledge of your WiFi password - very damaging for all of those who use mobile banking for instance! <=== Gust MEES: a MUST READ for anyone using m-Learning + "BYOD" and also any smartphone user... http://nakedsecurity.sophos.com/2012/10/02/what-is-your-phone-saying-behind-your-back/?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+nakedsecurity+%28Naked+Security+-+Sophos%29

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
As BYOD Trend Grows So Do Malware Attacks
The report found that the majority of employee’s devices did not have any form of security software loaded nor were company materials protected. The BYOD concept has been a growing trend for some years now as employees become more accustomed to using their own mobile computing devices in their jobs, and accessing corporate assets. The rapid adoption of high end smartphones and tablets including iPhones, iPads and Android devices along with the number of easily accessible apps is driving this concept forward. Cloud based services, accessible from almost anywhere, are also a key factor. The ‘Mobile Security Strategies: Threats, Solutions & Market Forecasts 2012-2017’ report report from Juniper found that while this trend can bring productivity benefits to businesses, it also poses potential security risks. In particular, the report found that the majority of employee’s phones and smart devices did not have any form of security software loaded nor were company materials protected. The new report provides detailed assessments of the mobile security threat and the growing market for security solutions. The war on cybercrime therefore continues for many organizations and especially their IT departments and CISOs. The total number of Computer viruses, trojans and web attacks is growing at their fastest pace in four years. Read more, a MUST: http://www.infosecisland.com/blogview/22364-As-BYOD-Trend-Grows-So-Do-Malware-Attacks.html?utm_source=dlvr.it&amp;utm_medium=twitter

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Coalfire recently conducted a survey on the BYOD to work trend. The findings reveal many companies are not discussing mobile device cybersecurity issues with their employees and lack policies to protect sensitive company data. The survey was conducted last month among 400 individuals in a variety of industries across North America that do not work in IT departments. “The BYOD trend is not slowing down, and while it has many benefits, it’s also introducing a number of new security risks that may be foreign to many companies,” said Rick Dakin, CEO and chief security strategist with Coalfire. ===> “The results of this survey demonstrate that companies must do much more to protect their critical infrastructure as employees work from their own mobile devices, such as tablets and smartphones, in the workplace. Companies need to have security and education policies in place that protect company data on personal devices.” <=== Read more, a MUST: http://www.net-security.org/secworld.php?id=13424
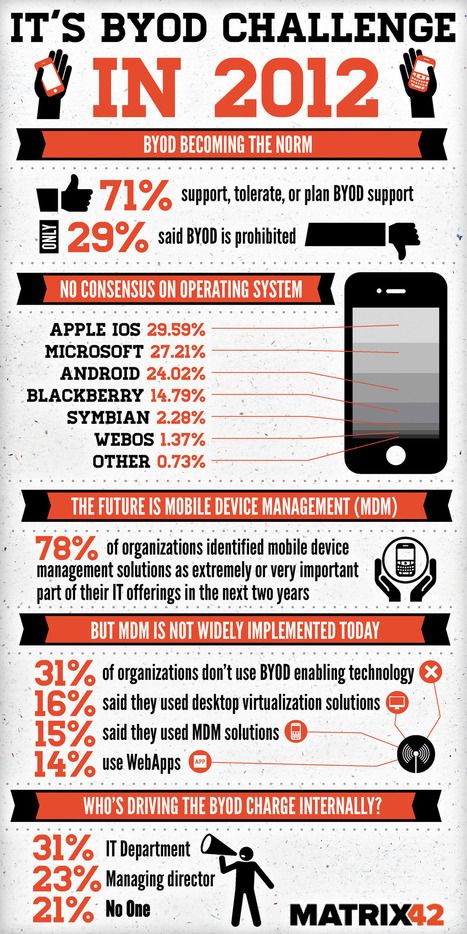
Bring your own device (BYOD) has become increasingly more prevalent in businesses with over 71% of companies planning, tolerating or supporting its infiltration into normal corporate work practices, according to an infograph published by Matrix 42. According to the below infograph the most common devices being utilised by employees via BYOD for work are laptops, PDA’s, mobile devices, and tablet computers. Simon Loughran one of Certification Europe’s leading ISO 27001 – Information Security Management Systems auditors published a paper called ‘Security and Mobile Devices’ on this topic recently. The paper identified one of the largest risk associated with the usage of BYOD devices such as mobile devices is inherent with their portability and that is precisely the intended functionality. Advanced technological changes allow people to work outside the corporate networks on wireless and remote connectivity, which in turn facilitates easily accessible and shareable company information. This creates a new risk area for companies as it has moved outside of the established security perimeter that has been so meticulously developed. The solution is to develop subsequent selected security controls around the mobile devices and BYOD devices which are as stringent as those employed around company devices. The Matrix 42 infograph was developed after the company completed a survey of 600 enterprise IT professionals and was published via Visual.ly. Top Ten tips for mobile security... Read moree, a MUST: http://www.certificationeurope.com/blog/byod-is-becoming-a-prevalent-information-security-and-it-management-focus/

|
Scooped by
Gust MEES
|
|
 Your new post is loading...
Your new post is loading...
 Your new post is loading...
Your new post is loading...
















![Online Trends and Risks with BYOD [pdf] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/k3ecoU08827ttk1VyHl7LTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)















Learn more:
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/