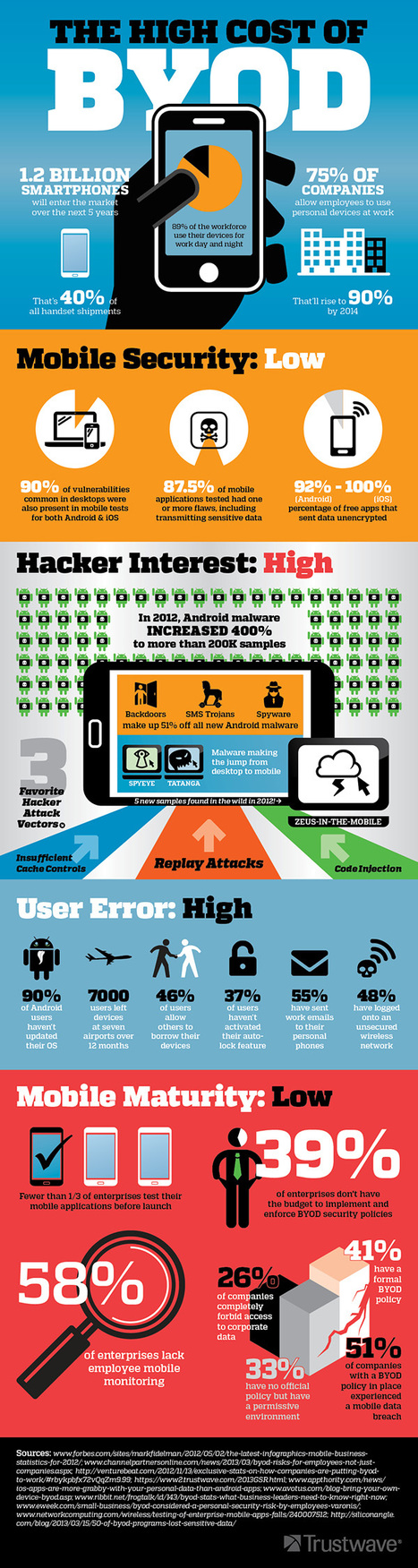
With the growth of BYOD, what security measures can IT take to ensure security of enterprise data – and does MDM have a role?
Research and publish the best content.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account
Already have an account: Login
Related articles to 21st Century Learning and Teaching as also tools...
Curated by
Gust MEES
 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
|

Ness Crouch's curator insight,
April 16, 2013 5:34 PM
Great explanation of Bring Your Own Device thinking. This can guide discussion about BYOD in schools. |












Learn more:
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/