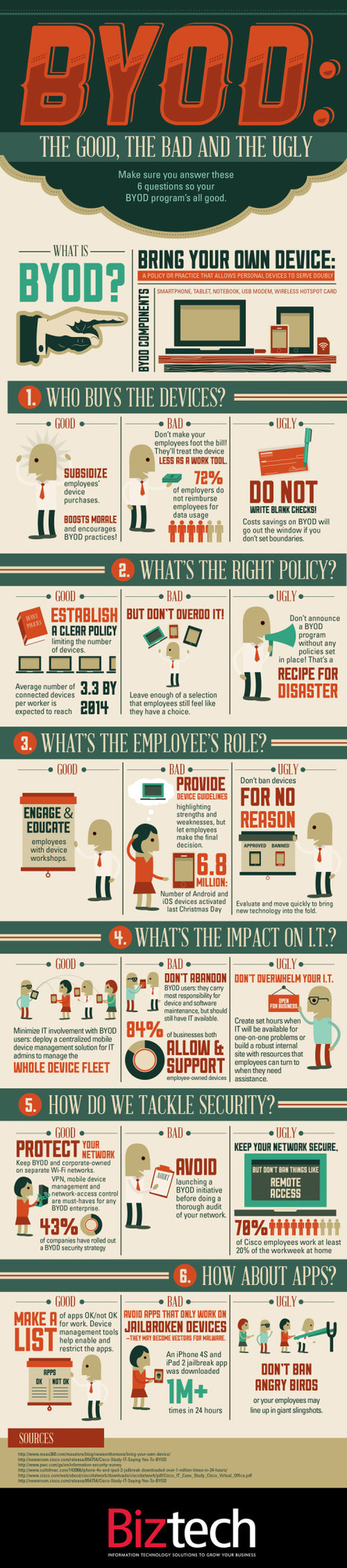
With the growth of BYOD, what security measures can IT take to ensure security of enterprise data – and does MDM have a role?
Research and publish the best content.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account
Already have an account: Login
Related articles to 21st Century Learning and Teaching as also tools...
Curated by
Gust MEES
 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...

Erica Cruz's curator insight,
October 20, 2015 2:45 PM
This article made me think about what are my school policies and guideline for safe use of a mobile device at school. |

Gust MEES's comment,
September 9, 2012 3:54 PM
Bonsoir,
Merci pour avoir fait lke #rescoop de ma curation, mais: Quand on #rescoop un article d'un autre curateur on le fait à 100% et on ne fait pas de la censure sur le #scoopit de cet auteur !!! Le texte complet est sur cette curation, voici ce qui manque: "===> Rogue IT is innovative and efficient for workers, but it’s becoming a real problem for IT managers. Here are four trends that are shaking up IT: <=== Gust MEES: check out also my FREE course about it here - http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/"; Et c'est l'article complet que je veux voir avec mes remarques personnelles, et rien d'autre !!! Si vous n'êtes pas d'accord avec mes remarques personnelles je vous conseille vivement d'effacer ce #scoopit (il est marqué avec mon nom !!!) et de prendre l'adresse originaire de le republier avec votre propre nom sans mes commentaires !!! J'espère que l'on s'est bien compris, autrement j'attends votre commentaire de retour !!! Bonne soirée, Gust 
Stéphane Koch's comment,
September 10, 2012 2:24 AM
Cher Gust, la "curation de contenu" est basée sur la mise à disposition de contenus que l'on aura auparavant "éditorialisés", l'idée étant d'organiser et de structurer l'information afin d'en offrir une "meilleure" lisibilité. Scoopit offre, par son champs d'édition, la possibilité d’aménager/organiser l'information à sa convenance... Que l'on partage, ou repartage une info... Concernant spécifiquement cet article ont je me permets - gentiment - de rappeler que vous n'en êtes pas l'auteur. Et d'ajouter qu'il n'y avait aucune volonté de censure de ma part... La mention de votre nom fait référence à la source de ce partage, et ne vous indique en aucune cas comme étant une référence par rapport au contenu de cet article, sur lequel par ailleurs vous n'avez aucun droit de propriété, si ce n'est celui d'être justement mentionné comme source dudit partage. Ni ne vous engage juridiquement. Vous devriez plutôt prendre en compte que la mention de votre nom permet aux lecteurs de venir visiter votre propre scoopit et de s'y abonner le cas échéant, et au final d'en apprendre plus sur vous et les différents services que vous offrez... Donc s'il y avait eu une volonté de "censure" de ma part, j'aurais "rescoopé" directement l'article sans mention de l'origine de son partage, d'autant plus que dans le cas présent je n'ai pas altéré ou modifié le contenu de l'article lors de sa "réédition".
Bref, si vous n'aviez pas utilisé un ton aussi peu courtois, j'aurais accédé avec plaisir à votre demande... Je vais donc laisser les choses en l'état, étant donné que - comme mentionné précédemment - cela permettra non seulement aux lecteurs intéressés d'accéder à votre scoopit, mais aussi de lire votre commentaire, et par conséquent, ce que vous vouliez communiquer.... Voilà pour ce qui est de mon "commentaire de retour". Pour finir, je ne peux m'empêcher de "quoter" "2001: A Space Odyssey (1968)". Je pense que c'est tout à fait approprié à la situation ;) "Look Dave, I can see you're really upset about this. I honestly think you ought to sit down calmly, take a stress pill, and think things over." |





















Learn more:
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/