Your new post is loading...
 Your new post is loading...
Equity and privacy problems with online proctoring reflect a larger issue: Students look to universities to set an example of integrity.
The Internet is an invaluable resource for teachers and students, but it's also one that's filled with risks as well. The education sector is commonly targeted by hackers, both because it has valuable data and because cyber security measures are inconsistent across districts, campuses, and buildings. They are prime targets for social engineering attacks such as phishing, since cyber security awareness may not be the same among the teacher and student population. Social engineering tactics can be particularly useful against larger organizations, as it's less likely that an unfamiliar face or name would be out of place in that environment. On top of that risk, a lack of privacy can also stem from inappropriate social media settings, over sharing, and other factors that lead to reputation damage or cyberbullying. Use this complete web browsing privacy guide to protect teachers, students, and parents from all the dangers of web browsing.
CHICAGO — Colleges are increasingly using Big Data to monitor students, control their access to information and set them on learning paths they may not have chosen, argues Chris Gilliard, a professor at Macomb Community College, who says the practices add up to “digital redlining.”
“I don’t think education is a predictive task,” said Gilliard, criticizing the use of data systems that allegedly forecast student success or failure. “I’m seeing a whole lot of wreckage in the process that people aren’t considering.”
Editor’s Note: We first quoted Caltech Artist-in-Residence David Kremers maxim, “Privacy is the new luxury” back in 2009. In the decade since then, we’ve seen a continuous assault on personal privacy, as surveillance has become the dominant business model on the internet. We’ve approached questions of privacy from many different angles over the years here at The Scholarly Kitchen, including technology architectural approaches to privacy (particularly relevant in light of new authentication systems like RA21), as well as striving to find the right balance between personalization and privacy).
Librarians have long been stalwart guardians of patron privacy — an increasingly difficult task in the era of Google and Facebook. Today’s post is by Mimi Calter, Deputy University Librarian for Stanford University, who brings a useful framework for libraries as they consider patron privacy.
Patron privacy has been a long-standing concern of libraries, and in the era of Facebook data-sharing scandals and of GDPR, the privacy of users of digital content is an increasing concern. In response to that general issue, and to several specific difficulties with data providers, Stanford Libraries, with support from a number of our peer institutions, have put forward a Statement on Patron Privacy and Database Access.
Social media can pose risks to students' privacy, but these risks can be managed with informed, intentional use. There's also a huge upside: Teachers can use social media to share best practices, provide an authentic audience for students' work, cultivate and model digital citizenship among their students and build more connected school communities.
Via EDTECH@UTRGV
Audrey Watters answers the question whether we’re ‘addicted’ to technology:
I am hesitant to make any clinical diagnosis about technology and addiction – I’m not a medical professional. But I’ll readily make some cultural observations, first and foremost, about how our notions of “addiction” have changed over time. “Addiction” is medical concept but it’s also a cultural one, and it’s long been one tied up in condemning addicts for some sort of moral failure. That is to say, we have labeled certain behaviors as “addictive” when they’ve involve things society doesn’t condone. Watching TV. Using opium.
I recently bashed Windows for being too darn snoopy, but you know what? It’s not just Windows. Ever since Yosemite came out, Apple’s macOS has been just as untrustworthy. As for Chrome OS, Android and iOS, come on! They’re all built around cloud services; by design, they share everything you do with third-party services. What’s the answer? Desktop Linux.
Collecting student data can be a great source of insight, but best practices for privacy and security must be followed.
The latest research from the Software & Information Industry Association (SIIA) shows that almost 70 percent of schools have seen a jump in data collection in the last few years. In K–12 schools, according to SIIA, administrators primarily use student data to track performance, improve instruction and keep parents updated on their child’s progress.
Protecting student privacy and making sure online environments are safe and secure in schools is a very big deal.
Next-gen security offers sophisticated web filtering technologies for higher education environments. While some colleges and universities may deploy web filtering to block internal users from accessing certain content or websites, more and more higher ed institutions are turning to increasingly sophisticated web filtering to handle a wide variety of external security threats, particularly with the advent of bring-your-own-device (BYOD) programs.
The Internet has become an essential tool for most of us and a part of our everyday lives. We rely on it to send/receive emails, post/share photos and messages on social networking sites, shop for ...
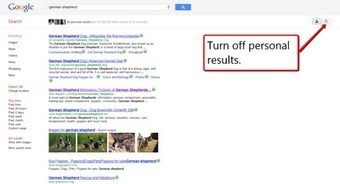
As you probably know, Google's privacy policies were recently overhauled. The data that Google collects about your use of their services (including the Chrome web browser) is now shared across all of Google's services. In other words, what you do with Chrome can be shared with Gmail, Google Music, or any of the other Google services you use. Why did they do this? The answer is simple: advertising. Google wants to be able to display the ads that they think will be most relevant to you.
|
"Like tens of thousands of other schools, Berkeley Unified School District in Northern California picked Zoom as its video-conferencing tool to support its remote instruction plan. But that came to a screeching halt after a naked adult “Zoombombed” one of its high school classes. A few days later the district switched to Google Meet, according to Ashley Boyd, whose two children—ages 9 and 12—attend school in Berkeley Unified."
Via EDTECH@UTRGV
Be Internet Awesome is a very good platform that teaches kids the fundamentals of digital citizenship and online safety. This is basically a program developed in collaboration between Google and other safety platforms such as Internet Keep Safe Coalition, ConnectSafely, and Family Online Safety Institute. Be Internet Awesome provides a wide variety of digital citizenship resources for kids, teachers and educators that include lesson plans, guidelines, classroom activities, and several other downloadable materials.
Whether you're new to Windows 10 or have been using it for years, take a minute to lock down your privacy.
Information about you, what you buy, where you go, even where you look is the oil that fuels the digital economy.
Michael Zimmer and Bonnie Tijerina
INTRODUCTION
The UW-Milwaukee Center for Information Policy Research, in partnership with Data & Society, along with the American
Library Association’s Offi ce of Intellectual Freedom and the New York Public Library, was awarded a National Leadership
Grants for Libraries award from the Institute of Museum and Library Services (IMLS) for the project “Library Values &
Privacy in our National Digital Strategies: Field guides, Convenings, and Conversations.” A series of gatherings were
held throughout 2017-2018 that brought together library practitioners, privacy advocates, and technology experts to
discuss and debate a national roadmap for a digital privacy strategy for libraries. The culminating event -- the Library
Values and Privacy Summit -- was held in New York City bringing together privacy experts from within and outside
libraries and sparked discussions on key privacy-related issues and possible paths forward.Click here to edit the content
It’s your profile, you can include what you want to include—right? Before you post, think. Are you prepared to have those words and images represent you for months, and even years to come? Your postings on profiles and to chats and blogs may have cyberlives much longer than what you might have imagined or intended, and may reach a much wider audience than you could have anticipated.
Stalkscan is the creepy name of a website that lets people enter the URL of a Facebook profile and view all of the public information for that profile. The site is a good reminder to check your Facebook privacy settings regularly.
Some might say that the Internet was built on anonymity, paving the way for a place where free speech reigns supreme.
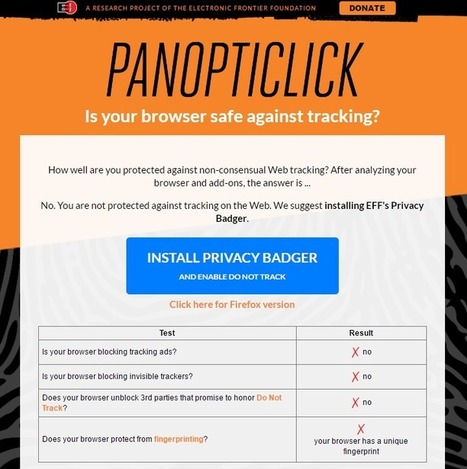
But after years of learning about who's snooping into everything we do online, privacy on the Web is a more popular topic than ever. But it's not just about government spying; it's also about how much big companies like Google, Facebook, and Microsoft have collected in order to serve up targeted ads.
She wanted to hide her pregnancy from big data. How hard could that be? Turns out hiding from Google and Facebook is almost impossible.
Whether you are new to computing or have some experience, Digital Literacy will help you develop a fundamental understanding of computers. The courses help you learn the essential skills to begin computing with confidence, be more productive at home and at work, stay safe online, use technology to complement your lifestyle, and consider careers where you can put your skills to work.and click “go”, and you will be taken to the appropriate page. Choose your language English (UK) & Welsh both available
Major innovations were few and far between in 2013. But 2014 promises a whole new world in tech. Here are 7 predictions.
|
 Your new post is loading...
Your new post is loading...
 Your new post is loading...
Your new post is loading...