 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Attackers could use critical firmware vulnerabilities discovered by Microsoft in some NETGEAR router models as a stepping stone to move laterally within enterprise networks.
The security flaws impact DGN2200v1 series routers running firmware versions before v1.0.0.60 and compatible with all major DSL Internet service providers.
They allow unauthenticated attackers to access unpatched routers' management pages via authentication bypass, gain access to secrets stored on the device, and derive saved router credentials using a cryptographic side-channel attack. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|
Lors de la conférence sur la sécurité RSA 2020 qui avait lieu la semaine dernière à San Francisco, les chercheurs en sécurité de la société slovaque antivirus ESET ont présenté des détails sur une nouvelle vulnérabilité qui affecte les communications WiFi.
Nommé Kr00k, ce bug peut être exploité par un attaquant pour intercepter et décrypter un certain type de trafic réseau WiFi (s'appuyant sur les connexions WPA2).
Selon ESET, Kr00k affecte tous les appareils compatibles WiFi fonctionnant sur des puces Wi-Fi Broadcom et Cypress. Ce sont deux des chipsets WiFi les plus populaires au monde, et ils sont inclus dans de nombreux appareils, allant des ordinateurs portables aux smartphones, et des points d'accès aux haut-parleurs intelligents et autres objets connectés. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/securite-pc-et-internet/?&tag=WLAN https://www.scoop.it/topic/securite-pc-et-internet/?&tag=Kr00k

|
Scooped by
Gust MEES
|
The FBI says owners of IoT (Internet of Things) devices should isolate this equipment on a separate WiFi network, different from the one they're using for their primary devices, such as laptops, desktops, or smartphones.
"Your fridge and your laptop should not be on the same network," the FBI's Portland office said in a weekly tech advice column. "Keep your most private, sensitive data on a separate system from your other IoT devices," it added.
The same advice -- to keep devices on a separate WiFi network or LAN -- has been shared in the past by multiple IT and security experts [1, 2, 3, 4].
The reasoning behind it is simple. By keeping all the IoT equipment on a separate network, any compromise of a "smart" device will not grant an attacker a direct route to a user's primary devices -- where most of their data is stored. Jumping across the two networks would require considerable effort from the attacker.
However, placing primary devices and IoT devices on separate networks might not sound that easy for non-technical users. The simplest way is to use two routers. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?tag=Smart+Home https://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/ https://www.scoop.it/t/securite-pc-et-internet/?tag=SHODAN+Search+Engine https://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things https://www.scoop.it/t/securite-pc-et-internet/?tag=smart-TV https://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things https://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/

|
Scooped by
Gust MEES
|
Over a million fiber routers can be remotely accessed, thanks to an authentication bypass bug that's easily exploited by modifying the URL in the browser's address bar.
The bug lets anyone bypass the router's login page and access pages within -- simply by adding "?images/" to the end of the web address on any of the router's configuration pages, giving an attacker near complete access to the router. Because the ping and traceroute commands on the device's diagnostic page are running at "root" level, other commands can be remotely run on the device, too.
The findings, published Monday, say the bug is found in routers used for fiber connections. These routers are central in bringing high-speed fiber internet to people's homes.
At the time of writing, about 1.06 million routers marked were listed on Shodan, the search engine for unprotected devices and databases. Half the vulnerable routers are located on the Telmex network in Mexico, and the rest are found on in Kazakhstan and Vietnam. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Router

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
This has got to be the quickest Quick Tip of all. Literally. With just one click, it’s too easy not to do.
You know your computer can be infected. But did you know your router can, too? And because most people just aren’t aware of it, if your router is compromised, it could stay that way a long time without you ever knowing.
Unless, of course, you use our free Router Checker. No need to download anything. Just visit the page and click to start the check. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|
More than 135 million modems are said to be vulnerable to a flaw that can leave users cut off from the internet -- just by someone clicking on a trick link.
The vulnerability, found in a modem used in millions of US households, can allow an attacker with access to the network to remotely reset the device, which wipes out the internet provider's settings and causing a denial-of-service attack. Every person and device on the network will permanently lose access to the internet until the modem owner contacts their internet provider.
READ THIS
2015's scariest data breaches: CVS, Anthem, IRS, and worse
Updated: Almost every American has been affected by at least one data breach this year.
Read More
The problem lies with how a widely-used modem, the Arris Surfboard SB6141, handles authentication and cross-site requests. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
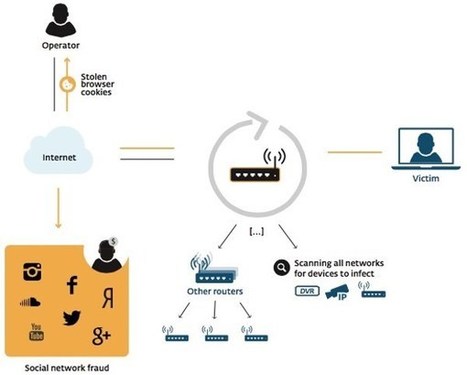
ESET researchers have issued a technical paper today, analysing a new worm that is infecting routers in order to commit social networking fraud, hijacking victims’ internet connections in order to “like” posts and pages, “view” videos and “follow” other accounts.
The malware, dubbed Linux/Moose by researchers Olivier Bilodeau and Thomas Dupuy, infects Linux-based routers and other Linux-based devices, eradicating existing malware infections it might find competing for the router’s limited resources, and automatically finding other routers to infect.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|
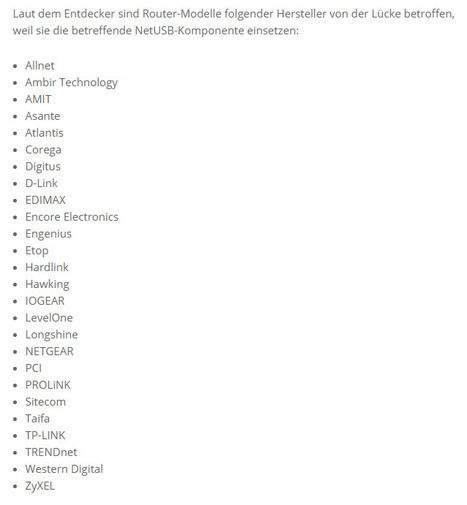
The security Expert Peter Adkins discovered a serious Information disclosure vulnerability that affects several Netgear wireless routers.
The researcher Peter Adkins discovered that several wireless routers produced by Netgear are affected by serious vulnerability that could allow an unauthenticated attacker to access sensitive data from the network device. By exploiting the vulnerability a hacker could also extract administrator passwords, the name and access keys for the wireless networks configured on the device, and details about the device including its model, firmware version and serial number, as explained in a post published on the Full Disclosure mailing list last week.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Router
|

|
Scooped by
Gust MEES
|
Certains malwares utilisent désormais le BSSID du point d’accès pour géolocaliser leurs victimes. Ils s’appuient pour cela sur des bases gratuites et accessibles à tous.
Le chercheur en sécurité Xavier Mertens a détecté une nouvelle méthode utilisée par les pirates pour géolocaliser leurs victimes et, le cas échéant, décider de leur sort. Habituellement, ils s’appuient sur l’adresse IP. Mais avec la pénurie d’adresses IPv4, il est de plus en plus difficile de géolocaliser cet identifiant avec certitude, car ces adresses sont de plus en plus échangées d’un opérateur à un autre et d’un pays à un autre.
Dans l’un des derniers codes malveillants analysés, Xavier Mertens a vu que l’auteur intégrait une seconde méthode : la géolocalisation par le BSSID (Basic Service Set Identifier). Cette séquence de 48 bits n’est rien d’autre que l’adresse MAC du point d’accès. Les 24 premiers bits désignent généralement le fournisseur. Les 24 bits restants sont choisis de telle manière à obtenir un identifiant unique de l’appareil. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|
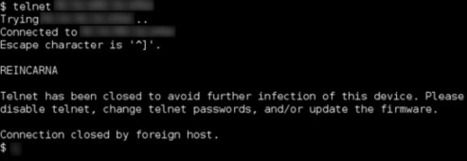
Einem Medienbericht zufolge hat ein Hacker 515.000 Zugangsdaten für Router, Server und Smart-Home-Geräte auf der ganzen Welt ausgespäht und in einem einschlägigen Forum für Cyberkriminelle veröffentlicht.
Datendiebstahl: Fernsteuerung möglich
Hacker mit entsprechenden Absichten und Kenntnissen sind mit diesen Informationen in der Lage, Schadsoftware auf die Geräte zu spielen und diese in der Folge fernzusteuern. Der Diebstahl erfolgte laut Bericht zwischen Oktober und November 2019. Selbst wenn sich seither IP-Adressen der Geräte geändert haben, sei es Hackern weiterhin möglich, mit ein wenig Aufwand an die neuen Daten zu gelangen. Um die Informationen aufzutreiben, bediente sich der Hacker einer Schwachstelle vieler Internet-Provider. Die konfigurieren Endgeräte oft falsch, sodass der sogenannte Telnet-Port für Angreifer sichtbar ist. Dabei handelt es sich um eine Schnittstelle zur Fernsteuerung von Geräten über das Internet.

|
Scooped by
Gust MEES
|
Security researchers have disclosed details today about 11 vulnerabilities known collectively as "Urgent11" that impact a wide range of devices, from routers to medical systems, and from printers to industrial equipment.
The vulnerabilities affect VxWorks, a real-time operating system created by Wind River.
Real-time operating systems (RTOSes) are simple pieces of software with very few features that are deployed on chipsets with access to a limited amount of resources, such as the chipsets used in modern Internet of Things (IoT) devices -- where the chipsets only need to manage input/output operations, with little data processing and no need for a visual interface.
Among all RTOS versions, VxWorks is today's most popular product, deployed on more than two billion devices, according to Wind River's website. However, in its 32-year history, only 13 security flaws with a MITRE-asigned CVE have been found in the VxWorks RTOS.
VxWorks' popularity and the lack of any attention from the security community were the two reasons why experts from IoT cybersecurity firm Armis decided to analyze the OS for security flaws, the company told ZDNet in a phone call last week. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/securite-pc-et-internet/?&tag=Urgent11 https://www.scoop.it/topic/securite-pc-et-internet

|
Scooped by
Gust MEES
|
Der Sicherheitsstandard WPA2, der insbesondere zur Verschlüsselung von WLAN-Netzwerken empfohlen wird, ist über kritische Schwachstellen verwundbar. Betroffen sind demnach alle derzeit aktiven WLAN-fähigen Endgeräte in unterschiedlichen Ausprägungen. Das Bundesamt für Sicherheit in der Informationstechnik (BSI) rät dazu, WLAN-Netzwerke bis zur Verfügbarkeit von Sicherheits-Updates nicht für Online-Transaktionen wie Online Banking und Online Shopping oder zur Übertragung anderer sensitiver Daten zu nutzen.
"Nutzen Sie Ihr WLAN-Netzwerk so, als würden Sie sich in ein öffentliches WLAN-Netz einwählen, etwa in Ihrem Lieblings-Café oder am Bahnhof. Verzichten Sie auf das Versenden sensibler Daten oder nutzen Sie dazu einen VPN-Tunnel. Auch das kabelgebundene Surfen ist weiterhin sicher. Unternehmen sollten ihre Mitarbeiter sensibilisieren und geeignete Maßnahmen zur Absicherung ihrer Firmennetzwerke ergreifen. Sicherheitsupdates wurden bereits von verschiedenen Herstellern angekündigt und sollten umgehend durch den Nutzer eingespielt werden, sobald sie zur Verfügung stehen," erklärt Arne Schönbohm, Präsident des BSI. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=VPN

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
135 million Arris modems are at risk of being knocked offline for between three and 30 minutes, because of an easily patchable vulnerability.
Security researcher David Longenecker explains that the SB6141 model Arris (formerly Motorola) SURFboard modem, one of the most popular cable modems in the world with 135 million currently in production, is vulnerable to unauthenticated reboot attacks due to two flaws.
The first issue is quite basic: the user interface for the modem has absolutely no authentication set up. Astonishingly, this allows a local attacker to look up 192.168.100.1 and access the administration web interface without entering a username and password. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Router

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Attackers have installed malicious firmware on nearly 200 Cisco routers used by businesses from over 30 countries.
|



 Your new post is loading...
Your new post is loading...









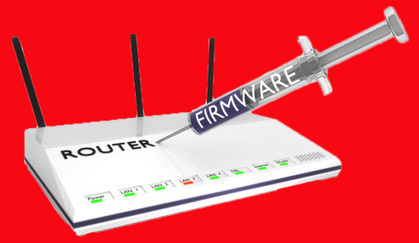

















Attackers could use critical firmware vulnerabilities discovered by Microsoft in some NETGEAR router models as a stepping stone to move laterally within enterprise networks.
The security flaws impact DGN2200v1 series routers running firmware versions before v1.0.0.60 and compatible with all major DSL Internet service providers.
They allow unauthenticated attackers to access unpatched routers' management pages via authentication bypass, gain access to secrets stored on the device, and derive saved router credentials using a cryptographic side-channel attack.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/securite-pc-et-internet/?tag=Router