 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
What could be more horrifying than knowing that a hacker can trick the plane's electronic systems into displaying false flight data to the pilot, which could eventually result in loss of control?
Of course, the attacker would never wish to be on the same flight, so in this article, we are going to talk about a potential loophole that could allow an attacker to exploit a vulnerability with some level of "unsupervised" physical access to a small aircraft before the plane takes off.
The United States Department of Homeland Security's (DHS) has issued an alert for the same, warning owners of small aircraft to be on guard against a vulnerability that could enable attackers to easily hack the plane's CAN bus and take control of key navigation systems.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/securite-pc-et-internet/?&tag=Airlines

|
Scooped by
Gust MEES
|
VW bugs: "Unpatchable" remote code pwnage
Two security researchers have excoriated Volkswagen Group for selling insecure cars. As in: hackable-over-the-internet insecure.
They broke into a recent-model VW and an Audi, via the cars’ internet connections, and were able to jump from system to system, running arbitrary code. Worryingly, they fully pwned the unauthenticated control bus connected to some safety-critical systems—such as the cruise control.
But VW has no way to push updates to its cars, and won’t alert owners to visit a dealer for an update.
Yes, it’s the internet of **** again: Potentially safety-critical bugs caused by the conflict between convenience and security. In this week’s Security Blogwatch, we prefer classic, analog vehicles.
Your humble blogwatcher curated these bloggy bits for your entertainment. Not to mention: Globfinity War…
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cars https://www.scoop.it/t/securite-pc-et-internet/?&tag=iot

|
Scooped by
Gust MEES
|
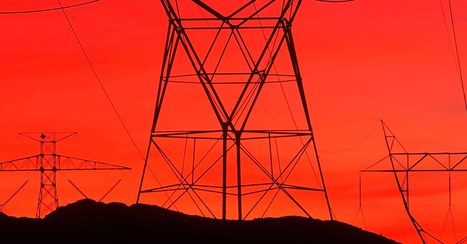
Nation-state attackers are attempting to undermine trust in critical services -- so how do we go about stopping them?
While cyber-attacks focusing on stealing email or other data are still very much part of the threat landscape, some of the most advanced hacking operations are focusing on grander goals.
Some of these groups -- almost all nation-state backed -- are turning their attention to critical infrastructure including utilities firms and power plants, while others are attempting to manipulate public attitudes and even elections through the use of fake news and other social media propaganda.
"It's not so much an attack on critical infrastructure, but rather an attack on the confidence and psychology of a nation," said Chris Inglis, former deputy director of the National Security Agency, speaking at World Cyber Security Congress event in London.
Attacking critical infrastructure and spreading disinformation is a powerful combination: after all, the reason that governments exist is to make sure the citizens of a country remain safe. Such tactics have been tried out in Ukraine over the last few years. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
|
Hackers -- possibly Russian -- have reportedly had access to the German government's secure network for over a year.
As first revealed by German news agency DPA, the hackers were able to steal data in the intrusion, which was apparently spotted in December.
The report quoted unnamed sources as saying the chief suspect is the notorious APT28 or Fancy Bear group, which was reportedly behind the German parliament's big 2015 hacking and, months later, the Democratic National Committee (DNC) compromise in the US.
Fancy Bear is widely believed to be under the Kremlin's control. Apart from the Bundestag and DNC, its targets have included everyone from the Ukrainian military and US defense contractors, to Russian opposition parliamentarians and the Putin-critical punk group Pussy Riot.
The group's previous German hack involved the Bundestag's regular network. This time it's the secure Berlin-Bonn Information Network (IVBB), an intranet run by the Interior Ministry that comes with higher usage restrictions for users and is supposed to be firewalled to the gills. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
|
Over the weekend, officials from the Winter Olympics taking place in South Korea confirmed a cyberattack hit systems helping run the event during the opening ceremony. They didn't provide much detail, though the attack coincided with 12 hours of downtime on the official website, the collapse of Wi-Fi in the Pyeonchang Olympic stadium and the failure of televisions and internet in media rooms, according to reports.
Researchers from Cisco's Talos cybersecurity unit now believe with "moderate" confidence they've found the malware responsible. They've suitably named it Olympic Destroyer, for its main focus is taking down systems and wiping data, rather than stealing information. More specifically, it deletes files and their copies, as well as event logs, whilst using legitimate features on Windows computers to move around targeted networks.
For the latter, the malware tries to use PsExec and Windows Management Instrumentation, both used by network administrators to access and carry out actions on other users' PCs. Both were used by the NotPetya ransomware in 2017. Whilst no one has attributed the Olympics attacks, Ukraine blamed Russia for NotPetya and suspicions the latter would target the event via digital means have been rife. Russia, meanwhile, has told media it was not responsible.
"We know that Western media are planning pseudo-investigations on the theme of 'Russian fingerprints' in hacking attacks on information resources related to the hosting of the Winter Olympic Games in the Republic of Korea," the foreign ministry said, according to the BBC. "Of course, no evidence will be presented to the world." Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet

|
Scooped by
Gust MEES
|
Symantec has warned of a new attack campaign targeting energy firms, which may have already given the hackers access to operational systems in the US and Europe.
The security giant claimed the Dragonfly threat group is behind the new round of attacks, ongoing since December 2015.
Organizations in the US, Turkey and Switzerland were identified as targets for a range of tools and techniques including malicious emails, watering hole attacks and trojanized software.
Emails with content specific to the energy sector were designed to socially engineer the recipients into opening a malicious attachment. If opened, they would steal the victims' network credentials.
Watering hole attacks were also used to harvest credentials, with the hackers booby-trapping sites likely to be visited by energy sector workers.
The stolen credentials were then typically used in follow-on attacks designed to install backdoors to provide remote access and give the hackers the option of installing additional tools. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=GRID http://www.scoop.it/t/securite-pc-et-internet/?&tag=Dragonfly

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
The U.S. Energy Department says the electricity system "faces imminent danger" from cyber-attacks, which are growing more frequent and sophisticated, but grid operators say they are already on top of the problem.
In the department’s landmark Quadrennial Energy Review, it warned that a widespread power outage caused by a cyber-attack could undermine "critical defense infrastructure" as well as much of the economy and place at risk the health and safety of millions of citizens. The report comes amid increased concern over cybersecurity risks as U.S. intelligence agencies say Russian hacking was aimed at influencing the 2016 presidential election.
"Cyber threats to the electricity system are increasing in sophistication, magnitude, and frequency," it said in the 494-page report. "The current cybersecurity landscape is characterized by rapidly evolving threats and vulnerabilities, juxtaposed against the slower-moving deployment of defense measures." Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/

|
Scooped by
Gust MEES
|
Despite spending more money on security than ever, organisations struggling with a widespread cybersecurity skills gap are often told how technologies like big data, analytics, machine learning, and artificial intelligence can aid them in protecting their data or critical infrastructure from attackers.
Organisations ranging from startups to established large corporations are investing in the building of AI systems to bolster defences by analysing vast amounts of data and helping cybersecurity professionals identify far more threats than would be possible if they were left to do it manually.
But the same technologies that improve corporate defences could also be used to attack them. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberattacks http://www.scoop.it/t/securite-pc-et-internet/?tag=Artificial+Intelligence

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Developers with both Mozilla and Tor have published browser updates that patch a critical Firefox vulnerability being actively exploited to deanonymize people using the privacy service.
FURTHER READING
Firefox 0-day in the wild is being used to attack Tor users
"The security flaw responsible for this urgent release is already actively exploited on Windows systems," a Tor official wrote in an advisory published Wednesday afternoon. "Even though there is currently, to the best of our knowledge, no similar exploit for OS X or Linux users available, the underlying bug affects those platforms as well. Thus we strongly recommend that all users apply the update to their Tor Browser immediately." Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=TOR

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
MyHeritage, an Israeli DNA, and genealogy website has suffered a massive data breach in which email accounts and hashed passwords of 92 million users (92,283,889) who signed up to the service up to October 26, 2017, have been stolen.
The compromised MyHeritage data was discovered by a security researcher on a private server outside of MyHeritage and reported the incident to the company who after an in-depth analysis acknowledged the breach and published an official statement on June 4, 2018. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyber-Attacks

|
Scooped by
Gust MEES
|
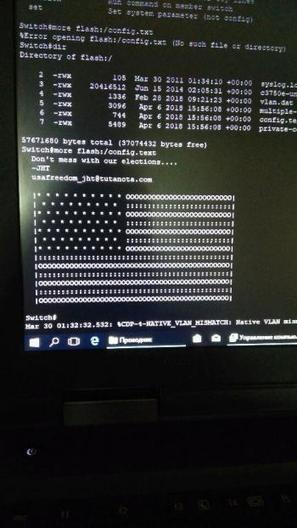
Unbekannte haben eine Sicherheitslücke in Cisco-Routern ausgenutzt und auf Systemen in Russland und Iran eine politische Botschaft hinterlassen. In westlichen Ländern hingegen schlossen sie die Lücke - behauptet zumindest eine anonyme E-Mail.
Hacker mit Sympathie für die USA nehmen für sich in Anspruch, am vergangenen Freitag zahlreiche Computersysteme in Russland und dem Iran über eine Sicherheitslücke gekapert und eine Abbildung der amerikanischen Flagge hinterlassen zu haben – zusammen mit dem Warnhinweis: "Don't mess with our elections..." (zu deutsch etwa: Mischt euch nicht in unsere Wahlen ein). Das meldet das Online-Magazin Motherboard.
"Don't mess with our elections..." Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
|
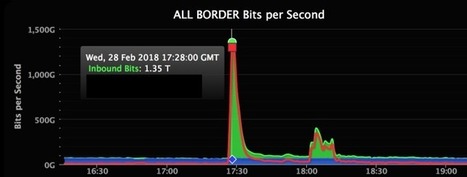
In a growing sign of the increased sophistication of both cyber attacks and defenses, GitHub has revealed that this week it weathered the largest-known DDoS attack in history.
DDoS — or distributed denial of service in full — is a cyber attack that aims to bring websites and web-based services down by bombarding them with so much traffic that their services and infrastructure are unable to handle it all. It’s a fairly common tactic used to force targets offline.
GitHub is a common target — the Chinese government was widely suspected to be behind a five-day-long attack in 2015 — and this newest assault tipped the scales at an incredible 1.35Tbps at peak.
In a blog post retelling the incident, GitHub said the attackers hijacked something called “memcaching” — a distributed memory system known for high-performance and demand — to massively amplify the traffic volumes that were being fired at GitHub. To do that, they initially spoofed GitHub’s IP address and took control of memcached instances that GitHub said are “inadvertently accessible on the public internet.”
The result was a huge influx of traffic. Wired reports that, in this instance, the memcached systems used amplified the data volumes by around 50 times. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=DDos

|
Scooped by
Gust MEES
|
GitHub has revealed it was hit with what may be the largest-ever distributed denial of service (DDoS) attack.
The first portion of the attack against the developer platform peaked at 1.35Tbps, and there was a second 400Gbps spike later. This would make it the biggest DDoS attack recorded so far. Until now, the biggest clocked in at around 1.1Tbps.
In a post on its engineering blog, the developer platform said that, on Feb. 28, GitHub.com was unavailable from 17:21 to 17:26 UTC and intermittently unavailable from 17:26 to 17:30 UTC due to the DDoS attack.
Github said that at no point "was the confidentiality or integrity of your data at risk. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
|
Phishing, Trojans, Ransomware and Viruses: Hardly a day goes by without hacker attacks against companies or private individuals. This huge LUCY Infographic shows the explosion of internet crime State of Cyber Crime 2018 – Numbers in detail In the United States by Internet crime caused damage in 2001:17.8 million USD. In the United …

|
Scooped by
Gust MEES
|
Hackers who hit American utilities this summer had the power to cause blackouts, Symantec says. And yes, most signs point to Russia. IN AN ERA of hacker attacks on critical infrastructure, even a run-of-the-mill malware infection on an electric utility’s network is enough to raise alarm bells. But the latest collection of power grid penetrations went far deeper: Security firm Symantec is warning that a series of recent hacker attacks not only compromised energy companies in the US and Europe but also resulted in the intruders gaining hands-on access to power grid operations—enough control that they could have induced blackouts on American soil at will.
Symantec on Wednesday revealed a new campaign of attacks by a group it is calling Dragonfly 2.0, which it says targeted dozens of energy companies in the spring and summer of this year. In more than 20 cases, Symantec says the hackers successfully gained access to the target companies’ networks. And at a handful of US power firms and at least one company in Turkey—none of which Symantec will name—their forensic analysis found that the hackers obtained what they call operational access: control of the interfaces power company engineers use to send actual commands to equipment like circuit breakers, giving them the ability to stop the flow of electricity into US homes and businesses.
Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=GRID

|
Scooped by
Gust MEES
|
Unidentified hackers have been targeting the networks of companies responsible for operating nuclear power plants in the US for the last two months, according to The New York Times. Citing a joint report issued by both the Department of Homeland Security and the FBI some time last week, The Times’ story identifies one target as the Wolf Creek Nuclear Operating Corporation, a facility responsible for overseeing the operation of a nuclear power plant outside Burlington, Kansas. The report also states that energy companies and manufacturing plants are also being targeted, yet none are identified by name. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
|
The stakes couldn’t be any higher in the global cybersecurity arena.
From Russia’s alleged role in the DNC hacks to this month’s revealing Vault 7 leak of nearly 9,000 CIA documents, it should now be clear that keeping data safe is of paramount importance for any organization. Leaks and hacks are causing irreparable damage across the board – and it is now more essential than ever before for individuals, organizations, and countries to be aware of common cybersecurity threats and how to prevent them.
IS YOUR COUNTRY PREPARED FOR CYBER ATTACKS?
Today’s infographic comes to us from CompariTech, and it breaks down the countries most prepared for cyber attacks, as well as those that are the most susceptible targets for cyber criminals. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
|
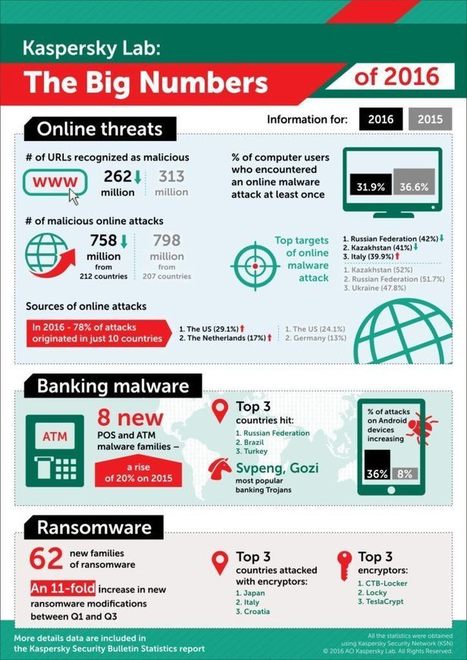
2016 was a tense and turbulent year in cyberspace – from the massive IoT botnets and ransomware to targeted cyberespionage attacks, financial theft... Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/

|
Scooped by
Gust MEES
|
Yahoo has disclosed that more than one billion accounts may have been stolen from the company's systems in another cyberattack.
The company said in a statement Wednesday after the markets closed that unnamed attackers stole the accounts in August 2013, a little over a year prior to a previously disclosed attack in September, in which attackers stole around 500 million accounts in 2014.
But the company said it wasn't able to identify the intrusion associated with August breach.
The statement said that the hackers may have stolen names, email addresses, telephone numbers, hashed passwords (using the weak, easy to crack MD5 algorithm) dates of birth, and in some cases encrypted or unencrypted security questions and answers.
Yahoo said it has invalidated unencrypted security questions and answers so that they cannot be used to access affected accounts.
But payment card data and bank account information, stored in separate systems, are not thought to have been stolen in the attack. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Yahoo... http://www.scoop.it/t/securite-pc-et-internet/?tag=DATA-BREACHES http://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberattacks

|
Scooped by
Gust MEES
|
Every day we seem to hear about new data breaches. Every day users are warned that their personal information may have been exposed, that they should reset their passwords, and tighten their security measures to prevent hackers from exploiting their details.
Today the concern is related to one of the world’s biggest video platforms. Dailymotion, where users upload, watch and share videos, has reportedly been hacked and the details of approximately 85 million users exposed.
Breach notification service LeakedSource, which most recently brought a mega breach at AdultFriendFinder to the public’s attention, obtained the data after the breach which is thought to have happened in October.
As ZDNet reports, the good news is that most of the leaked account details do not have passwords attached.
Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberattacks

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...













![State of Cyber Attacks 2018 – A big Overview about Cybercrime [Infographic] - LUCY Phishing, Social Hacking and Security Awareness | #CyberSecurity | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/dH0qjTsuLei_pVSG-kbkczl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)










What could be more horrifying than knowing that a hacker can trick the plane's electronic systems into displaying false flight data to the pilot, which could eventually result in loss of control?
Of course, the attacker would never wish to be on the same flight, so in this article, we are going to talk about a potential loophole that could allow an attacker to exploit a vulnerability with some level of "unsupervised" physical access to a small aircraft before the plane takes off.
The United States Department of Homeland Security's (DHS) has issued an alert for the same, warning owners of small aircraft to be on guard against a vulnerability that could enable attackers to easily hack the plane's CAN bus and take control of key navigation systems.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/topic/securite-pc-et-internet/?&tag=Airlines