Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Security researchers have discovered a new type of "Man-in-the-Middle" (MitM) attack in the wild targeting smartphone and tablets users on devices running either iOS or Android around the world.
The MitM attack, dubbed DoubleDirect, enables an attacker to redirect a victim’s traffic of major websites such as Google, Facebook and Twitter to a device controlled by the attacker. Once done, cyber crooks can steal victims’ valuable personal data, such as email IDs, login credentials and banking information as well as can deliver malware to the targeted mobile device.
San Francisco-based mobile security firm Zimperium detailed the threat in a Thursday blog post, revealing that the DoubleDirect technique is being used by attackers in the wild in attacks against the users of web giants including Google, Facebook, Hotmail, Live.com and Twitter, across 31 countries, including the U.S., the U.K. and Canada.

|
Scooped by
Gust MEES
|
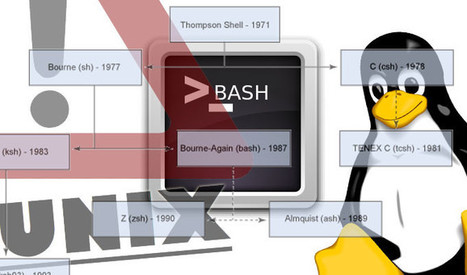
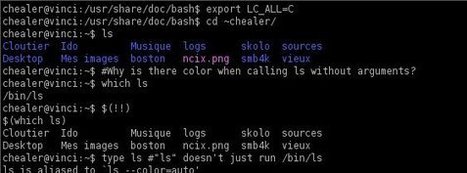
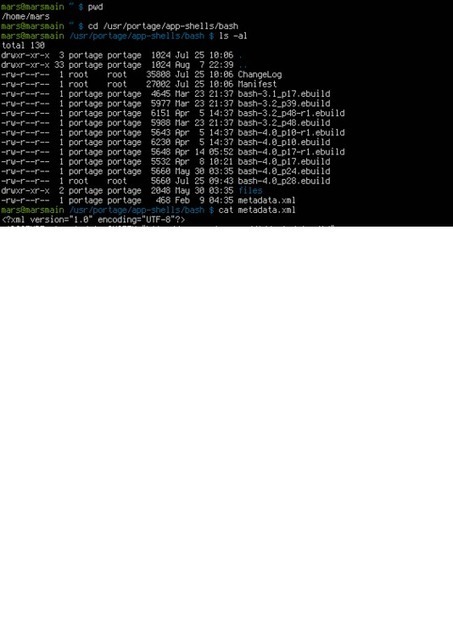
A critical vulnerability in the Bourne again shell, simply known as Bash and which is present in most Linux and UNIX distributions and Apple’s Mac OS X, has been discovered and administrators are being urged to patch immediately.
The flaw allows an attacker to remotely attach a malicious executable to a variable that is executed when Bash is invoked.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Bash+Command+Flaw

|
Scooped by
Gust MEES
|
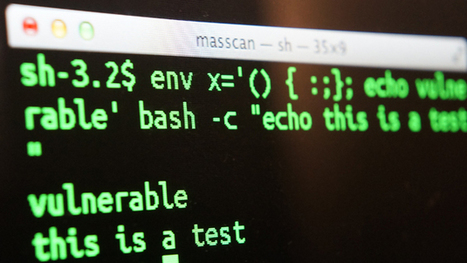
Security researchers have found the first malware using the new Bash bug.
Security researchers have found proof of concept code that attempts to exploit the serious bug discovered this week in Bourne-Again Shell, also known as Bash, which according to US CERT affects both Linux and Mac OS X.
The good news yesterday that some Linux distributions shipped patches for the bug yesterday has already been tempered by the discovery that those patches only partially dealt with potential attacks. In an update overnight, Red Hatsaid that it was developing a new patch, however, it is still advising users to apply the incomplete one for now. At the same time as security experts have been racing to develop fixes for the bug and patch systems, it appears hackers have been working on tools to attack vulnerable systems.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Bash+Command+Flaw

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Utrecht, le 27 novembre 2013 - Selon une récente enquête de Kaspersky Lab, il existe de fortes probabilités qu’un nombre croissant d’utilisateurs Mac soient la proie de menaces d’Internet. La quantité des logiciels malveillants ciblant les Mac a augmenté de 50% au cours des douze derniers mois. Pourtant, plus d’un tiers (35%) de tous les utilisateurs Mac pensent à tort être protégés contre les menaces numériques.
Le nombre des propriétaires de Mac continue de progresser, et par conséquent l’intérêt des cybercriminels pour cette plate-forme s’amplifie lui aussi. Les virus informatiques, chevaux de Troie, astuces de phishing et autres menaces d’Internet visant cette plate-forme sont d’ores et déjà en circulation, en grands nombres qui plus est. Les utilisateurs sont ainsi tout aussi vulnérables que les utilisateurs de PC Windows.
Via Gust MEES
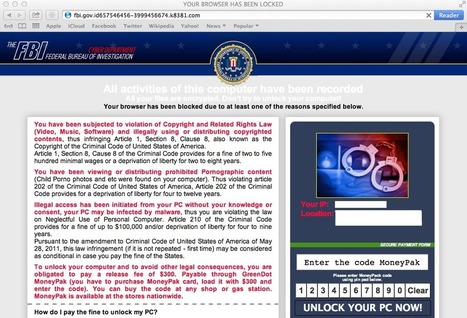
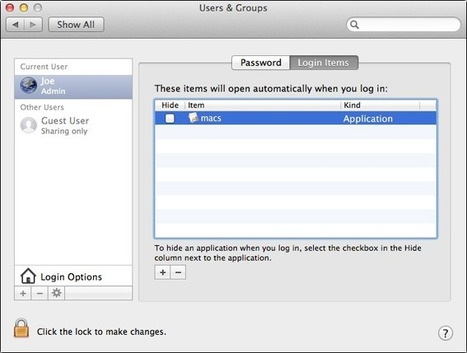
The FBI has become aware of the recent news regarding the ransomware that’s designed to target Mac OS X users. The agency’s Internet Crime...
Via Gust MEES
For years, Windows users have been plagued by ransomware demanding several hundred dollars to unlock their computers. Now there's a growing market to target Macs.
Via Gust MEES
The Oslo Freedom Forum is an annual event "exploring how best to challenge authoritarianism and promote free and open societies." This year's conference (which took place May 13-15) had a workshop for freedom of speech activists on how to secure their devices against government monitoring. During the workshop, Jacob Appelbaum actually discovered a new and previously unknown backdoor on an African activist's Mac.
Our Mac analyst (Brod) is currently investigating the sample.
It's signed with an Apple Developer ID.
Via Gust MEES
Macworld Australia is the premier Australian source for news, reviews, help, how-tos, and expert opinion for the Australian Apple market, including the Mac, iPhone, iPad, and iPod.
Via Gust MEES
Mat Honan got owned last year and it sucked, but you can still learn his lesson.
|

|
Scooped by
Gust MEES
|
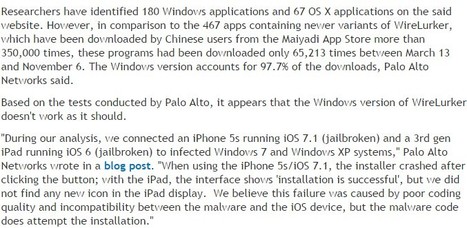
Researchers have pointed out an interesting aspect of the iOS malware. The threat contains binary code for 32-bit ARMv7, 32-bit ARMv7s, and 64-bit ARM64 architectures. This makes WireLurker the first iOS malware that targets the ARM64 architecture.
The Maiyadi App Store on which the initially discovered variants were hosted seems to be linked to the creators of the malware, Palo Alto said. One piece of evidence is the bundle identifier named "com.maiyadi.installer" in the OS X samples. The samples also include copyright information referencing Maiyadi.
The C&C servers user by WireLurker are currently inactive, and Apple has taken steps to ensure that its users are protected, including the revocation of the stolen code signing certificates used by the malware creators to run the malicious iOS apps on non-jailbroken devices.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security?q=wirelurker

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
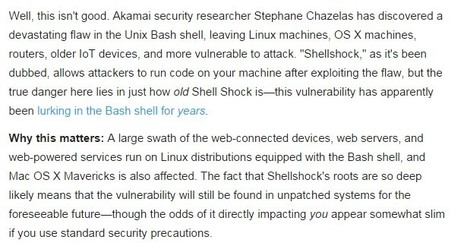
Et si je vous disais qu'il y a dans votre ordinateur un mouchard que vous ne pouvez pas enlever, qui a été mis en place par le constructeur, qui est sur les listes blanches de la plupart des antivirus et dont vous n'avez jamais entendu parler ? La société Kaspersky, spécialisée dans la détection et …
Via Frederic GOUTH, Gust MEES
About 860,000 members who post on the forums of popular Apple news website MacRumors are being asked to change their passwords after accounts were compromised in a hack.
Via Gust MEES
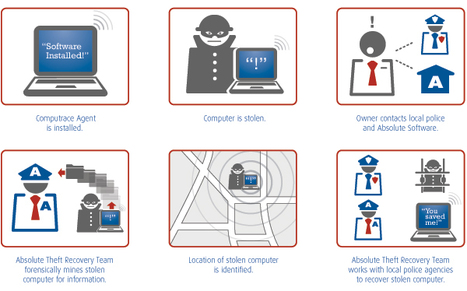
Mac backdoor Trojan takes advantage of Unicode's Right-to-Left marker to hide its true nature, steals screenshots and audio from infected computers.
Via Gust MEES
Patch Tuesday is coming on 11 June 2013.
Paul Ducklin gives you a quick preview of what we know so far, and who'll be affected by the updates...
(Mac users, that might include you.)
INFOGRAPHIE: Pourri jusqu'à l'os
Via Gust MEES

|
Scooped by
Gust MEES
|
Minority groups in China appear to have been targeted by a Mac malware attack, delivered via boobytrapped Word documents.
Who could possibly be interested in targeting their computers? It is true that there is much less malware for OS X than there is for Windows, but that's not going to make you feel any better if you end up targeted in an attack like this. Mac users, just like Windows users, need to ensure that they install the latest security patches and keep their software properly up-to-date. If you're not already doing so, run anti-virus software on your Macs. If you're a home user, there really is no excuse at all as we offer a free anti-virus for Mac consumers.
|




 Your new post is loading...
Your new post is loading...







![Hacking lessons learned: how to cover your digital ass [Infographic] | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/ATbLGoX1_LvhG_GpIt6fADl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)



![Pourri jusqu'à l'os [Infographic] | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/yrxY_sDewqzAEcP19KRYeTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)