Bring Your Own Device (BYOD) is more complex than most people know, read further to learn… . .
Keywords for this free course: . motivation, engagement, heroes, Security-Scouts, critical thinking, stay out of the box, adapt to new technologies, be aware of the malware, nobody is perfect, knowing the dangers and risks, responsibility, responsibility of School, responsibility of IT-Admin, responsibilities of BYOD users, Apple insecurity, Insecurity of Apps, Principals responsibilities, Mobile Device Management, risks of BYOD, BYOD-Policy, IT-Security Infrastructure, Teacher-Parents Meeting, Cyberwar, Cyberwarfare, Government, Internet-Safety, IT-Security knowledge basics...
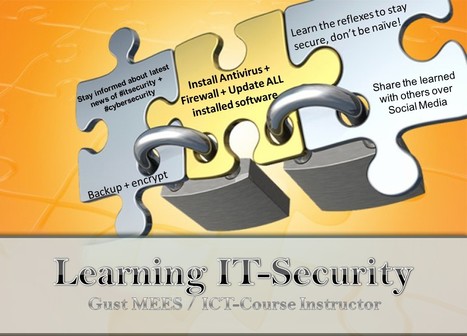
The weakest link in the Security Chain is the human! If you don’t respect certain advice you will get tricked by the Cyber-Criminals!
=> NOBODY is perfect! A security by 100% doesn’t exist! <=
Read more:
http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
Via
Gust MEES,
Lee Hall



 Your new post is loading...
Your new post is loading...











The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox.
The vulnerability allows hackers to modify an app without breaking its cryptographic signature, according to Jeff Forristal, chief technology officer (CTO) at mobile security firm Bluebox.
there is one example of smart phone security. focus on the mobile system Android